Identify data breaches before they happen…
Today, people typically share sensitive personal data with hundreds of organisations. It’s an essential part of modern life. But, it could put your business at risk.
Acuris CybercheckTM harvests compromised identity information from criminal forums on the unindexed web.
A common information security risk faced by all businesses is through staff using their email addresses for non-related business activities such as e-commerce, video streaming and even web-sites which look genuine but only exist to harvest personal information.
With Acuris CybercheckTM you can check and monitor key executives and wider staff; through your organisation’s corporate email domain(s); against the world’s largest proprietary database of compromised individual and business information to prevent account takeover, limit corporate exposure and enforce adherence to Information Security Policies.
Our strength
Why check with Acuris CybercheckTM?
Real depth
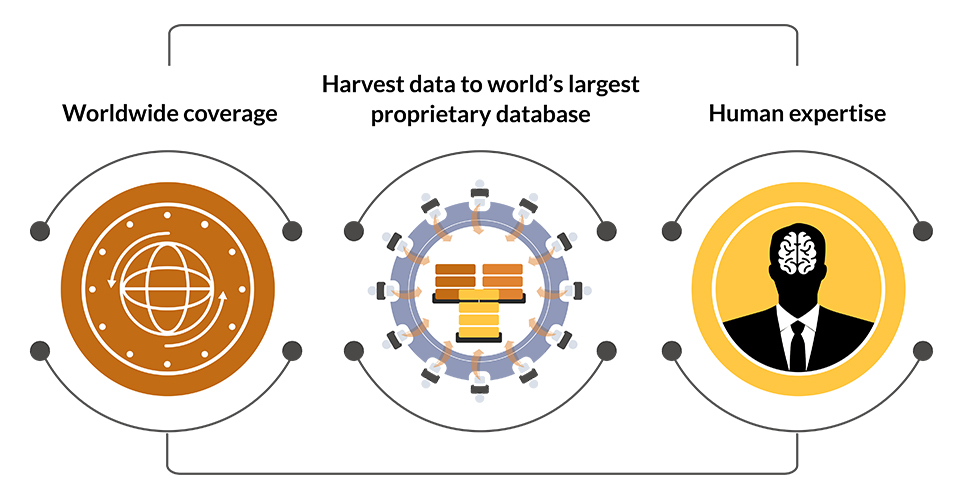
Our coverage is our strength.
Criminals are exploiting more and more types of sensitive information – we harvest the data that may be putting you at risk.
- Identity data
- Personal data
- Financial data
1000+
Criminal forums, websites and chatrooms monitored
Real expertise
Acuris CybercheckTM, use skilled experts with backgrounds in law enforcement to monitor the criminal internet. Their experience of criminal behaviour patterns gives Acuris CybercheckTM a unique advantage over machine-driven searching.
Protect your business
- Enhanced account takeover protection
- Limit corporate exposure
- Strengthen data privacy and breach disclosure compliance
- Provide evidence of potential data breaches
- Assess your exposure to fraud and phishing
Reinforce due diligence
- Assess data compromise in M&A and corporate transactions
- Improve risk assessments
- Take proactive measures against risk
$3.86 mn
Average cost of a data breach in 2018
With criminals exploiting all types of sensitive information, we harvest the data that may be putting you at risk, adding to the world’s largest proprietary database continually.
Protect your business from every angle.

- Monitor your company domain for employee breaches
- Benefit employees with identity theft monitoring
- Monitor third-party suppliers for breach exposure
- Reinforce due diligence
- Protection for your business